by admin | Nov 23, 2020 | Best Practices
At ThreatWarrior, we often collaborate on key projects. One that requires us to be aligned internally is our thinking on the core elements of our product strategy, or our design principles. First and foremost, everything we do as a company has one bottom-line...

by Jon Rubin | Nov 14, 2020 | Cybersecurity, Deep Packet Inspection
What is Continuous Deep Packet Inspection? Continuous deep packet inspection (DPI) is a powerful technique for inspecting and filtering network traffic. DPI evaluates the packet header and contents in order to identify malware and classify traffic by application...
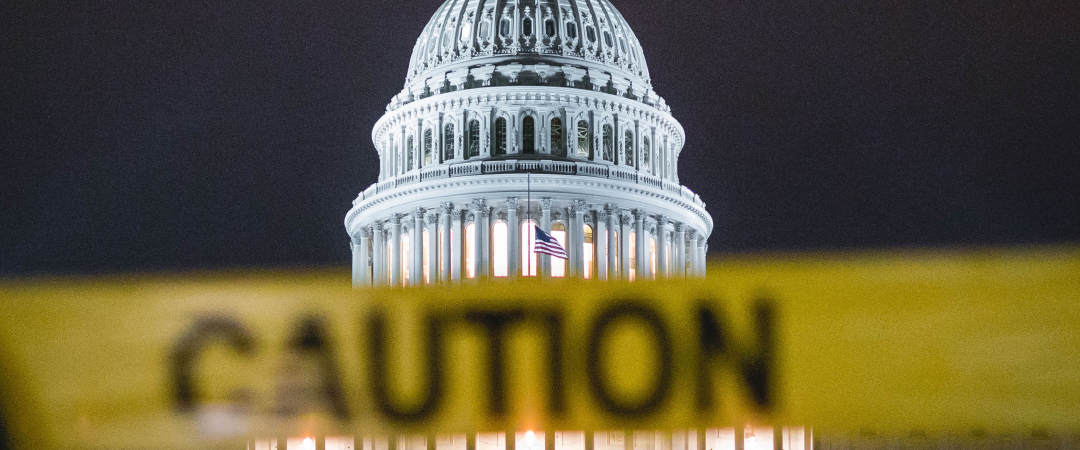
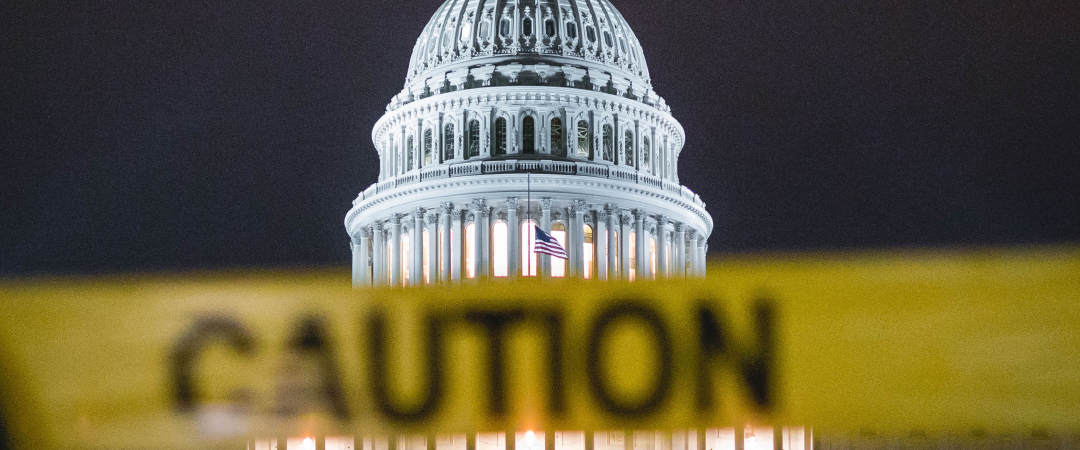
by Pete Slade | Mar 13, 2020 | Critical Infrastructure
The Cyberspace Solarium Commission (CSC) has released a report that suggests US cybersecurity policy is in need of drastic changes. The 182-page report is the result of a yearlong congressional study led by a bipartisan group of lawmakers. It calls for a policy...
by Pete Slade | Nov 7, 2018 | Threats
The Russian cyber attack on the 2016 Presidential Election has brought cybersecurity to the forefront. Regardless of which industry you’re in, that attack made it abundantly clear we’re all at risk of cyber breaches. But don’t kid yourself – it isn’t just foreign...

by Pete Slade | Oct 24, 2018 | Critical Infrastructure
The nation’s infrastructure is vulnerable to cyberattacks. We know this because a successful, prolonged (the attacks began as early as March 2016) cyberattack was discovered this year. In March 2018, the United States Department of Homeland Security (DHS) and the...