The Russian cyber attack on the 2016 Presidential Election has brought cybersecurity to the forefront. Regardless of which industry you’re in, that attack made it abundantly clear we’re all at risk of cyber breaches.
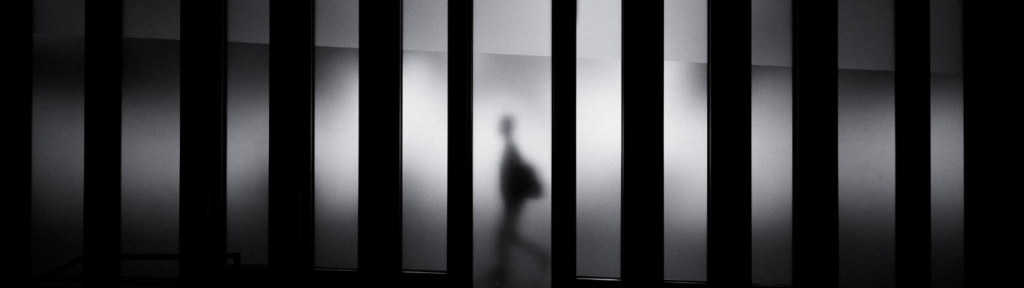
But don’t kid yourself – it isn’t just foreign powers or organized crime syndicates breaching organizations. Your data is also threatened by insiders – people who are already employed within the federal government, public organizations, private sector businesses, and academia.
No doubt you remember the case of Edward Snowden, a whistleblower who leaked sensitive secrets concerning government surveillance programs. Don’t forget Anthony Levandowski, a former employee of Alphabet, who allegedly stole 9.7 GB of confidential files from Waymo (Alphabet’s autonomous vehicle subsidiary) and gave them to his new employer – Uber.
Insider Threats Aren’t Always Malicious
Sure, there are plenty of cases like the above where an inside actor purposely breached systems or stole documents. However, many leaks caused by insiders aren’t done deliberately – they come from employees who carelessly open phishing emails that contaminate systems with malware.
Regardless of the intent of an insider breach, one thing is certain: they are dangerous, can cause massive damage and cost you a lot of money.
According to the 2018 Cost of Insider Threats: Global Organizations, a 12-month benchmark study, the mean cost of an insider threat is $8.7 million. The minimum cost is just shy of $500,000, while the maximum cost is a staggering $26.5 million. The report also found that organizational size and industry affect the cost per incident, with financial services firms and large organizations paying the most.
But the root cause of most insider incidents? Negligence, not malice. “Specifically, the careless employee or contractor was the root of almost 2,081 of the 3,269 incidents reported. The most expensive incidents are due to imposters stealing credentials and were the least reported.”
What/Who Causes Insider Threats?
The truth is, anyone the inside can cause a breach whether by mistake or not.
Most companies focus all their efforts on securing the perimeter but have no defense against internal threats. This leaves them blind to an insider threat, as they cannot track a cyber attack once it breaks through their firewall, nor can they detect suspicious activity that already exists on the network.
So, who is a suspect? Anyone could pose an insider threat, but who’s most likely to actually cause a breach (whether by innocent mistake or malicious intent)? Cybersecurity experts have identified three possible culprits:
- The trusted employee with wide-ranging access who intentionally or unintentionally misuses data
- A remote employee, a subcontractor, or a third-party vendor who has access to your system
- Disgruntled employees who want to retaliate against perceived slights or termination
There are a number of reasons why an employee might commit such a crime. They include:
- Personal Gain
- Revenge
- Political agenda
- An employee who is enticed by a competitor
- An employee who wants to begin a competing business
Preventing Insider Threats
Preventing insider threats requires visibility. How can you stop something you can’t see? With new technologies, cloud storage and IoT devices being used every day, there are more ways than ever for networks to be compromised. Here are a few tips on how to limit the potential for successful insider attacks:
- Rework your security policy. Make sure you limit access and privileges when possible. Detail who can access what data and under what circumstances and specify the consequences of misusing or mishandling data.
- Use multifactor authentication. How often do you see password-covered Post-it Notes on desks? How many times have employees shared passwords because it’s more convenient? Plus, password-cracking technology is more advanced than you might think. Simply put: passwords just aren’t enough anymore.
- Watch data movement. You must have visibility into the way data moves across your network; which devices communicate, how they communicate, what they communicate. It’s important that your solutions can also see data as it moves into and out of your organization, even onto devices or into the cloud.
- Monitor for rogue devices. Be wary of network-connected devices that have not been approved by your IT security team.
- Conduct regular security awareness training. Many insider breaches are caused by unwitting employees – people who click malicious links or download infected files because they didn’t know better. Utilize cybersecurity education to help insiders identify and ultimately mitigate phishing attempts.
We get it… easy passwords and reminders make your life more convenient. But don’t use over-simplified passwords or write them down where anyone can see them!
And, of course, don’t forget the basics. Perform background checks on all new employees, educate all employees on cybersecurity best practices, and limit privileged access to sensitive data. Monitor third-party access and closely govern their permissions.
TL;DR
Monitoring for insider attacks can seem daunting but it must be done. Access to your systems is necessary for employees to perform their jobs, but they can also be a threat – you have to protect inside the perimeter too. Limit access when possible and understand that threats may already be inside. Utilize solutions that give you visibility into your entire business because if you’re not watching what’s happening you’re asking for trouble.
It’s a zero-trust world; your network architecture better reflects that.