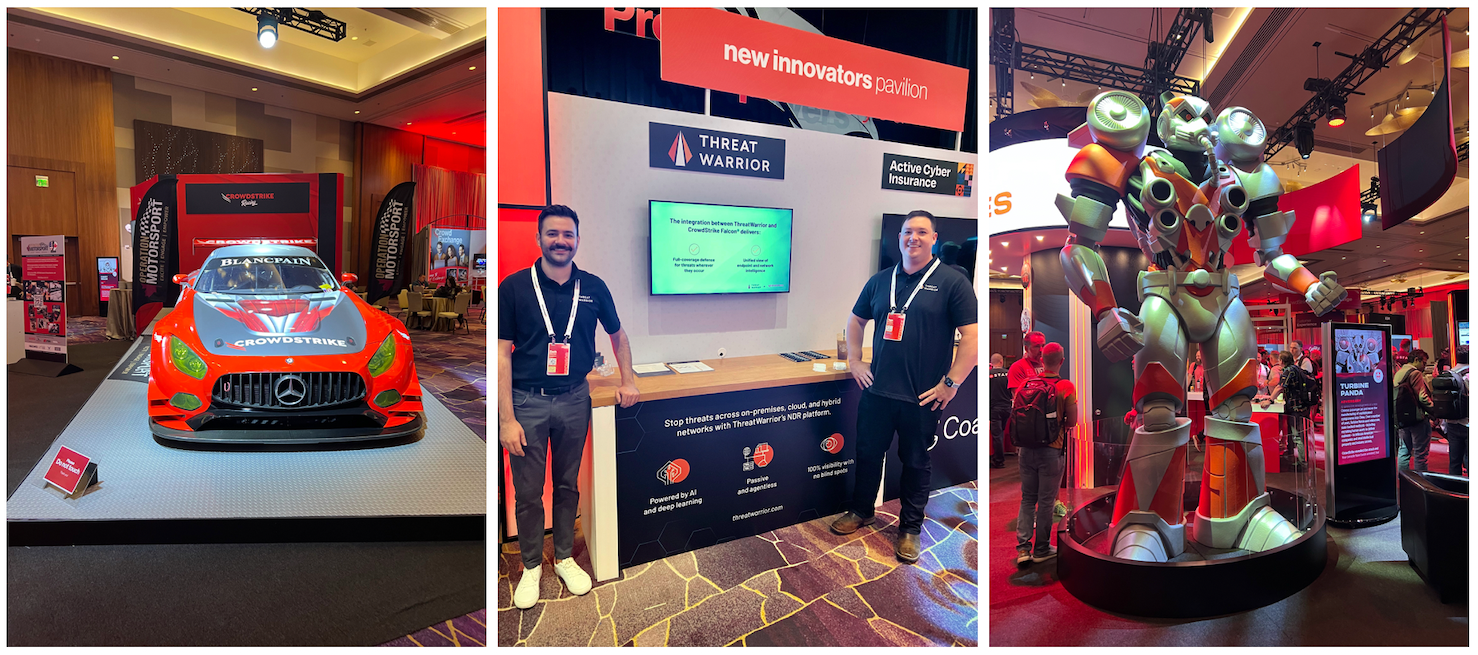
Last week, ThreatWarrior attended Fal.Con 2022 live in Las Vegas to connect with cybersecurity insiders, discuss how we work with CrowdStrike to extend threat protection across the enterprise, and share why network detection and response (NDR) is critical to any defense-in-depth strategy. We joined thousands of security and tech professionals worldwide for three days of experiential demos and content, cutting-edge keynotes, hands-on business and technical sessions, and so much more.
We were inspired by all of the CrowdStrike customers and security professionals we spoke with and we heard so many great questions about our platform, the future of cybersecurity, and how we help combat ever-increasing cyber risk.
Below are are some highlights of the questions we received.
What is Network Detection and Response (NDR)?
Many organizations are adopting network detection and response (NDR) solutions to strengthen their cybersecurity posture as they face the rise in ransomware, expanding IT infrastructures, and a shortage of cybersecurity talent. NDR is an emerging category of security product that combines rules and behavior-based techniques to analyze network traffic in real time to:
- Identify known and uncover unknown threats
- Identify behavioral patterns and anomalies
- Stop in-progress attacks before they become breaches
- Detect malicious activity in north-south and east-west corridors
While perimeter security, log analysis solutions, and endpoint detection and response (EDR) platforms are necessary, they leave blind spots across the enterprise. For example, many IoT technologies and connected devices like smart TVs or printers cannot support an EDR agent. Further, rogue or unauthorized devices would not have an endpoint agent installed on them and would therefore be invisible to an EDR solution.
NDR products do not require agents to deliver insight into malicious activity across on-premises, cloud, and hybrid environments.
How does NDR fit into an XDR strategy?
Network visibility and protection plays a critical role in security. Because NDR solutions gather intelligence directly from network data, they are able to deliver the real-time visibility needed to detect threats across the enterprise.
By combining NDR with EDR and SIEM technologies, you can gain insight and correlate intelligence from different sources to close security gaps. Without integrating NDR into your layered defense strategy, you may be completely blind to attacks that sneak past the perimeter or evade endpoint protection.
How does ThreatWarrior work with CrowdStrike?
 ThreatWarrior and CrowdStrike work together to extend threat protection across the enterprise from the network to the endpoint. The integration correlates threat intelligence and adds context to alerts with network and endpoint telemetry. By providing unified intelligence and complete visibility, we help users identify and stop threats faster.
ThreatWarrior and CrowdStrike work together to extend threat protection across the enterprise from the network to the endpoint. The integration correlates threat intelligence and adds context to alerts with network and endpoint telemetry. By providing unified intelligence and complete visibility, we help users identify and stop threats faster.
The combination of ThreatWarrior and CrowdStrike Falcon also delivers an always-up-to-date asset inventory so you can identify every connection including managed, unmanaged, rogue devices, IoT, and other devices without endpoint protection.
You can learn more about ThreatWarrior’s integration with CrowdStrike here.
Can ThreatWarrior protect IoT and OT?
Yes, ThreatWarrior can see and protect anything that touches your network, including IoT devices, operational technology, Industrial Control Systems, and much more. We help our clients increase their operational resilience by arming them with a current asset inventory and asset discovery, fortifying their network security, and enabling them to detect and respond to threats immediately.
Because ThreatWarrior harnesses the power of network intelligence, we are able to see and protect legacy technology, OT, SCADA, and other systems that cannot support an endpoint agent.
Does ThreatWarrior provide an asset inventory even on devices without a CrowdStrike agent?
ThreatWarrior identifies and analyzes every network connected “thing.” Even if a device is not yet protected by endpoint security, ThreatWarrior will see it communicating on the network, help you understand it’s behavior, and enable you to determine whether it should be there or not. This includes new connections, unmanaged devices, and more.
__________________
A big thank you to CrowdStrike for hosting us, and another for all of the security professionals who stopped by to see us and talk about ThreatWarrior. We’re already looking forward to seeing you again next year!
Do you have additional questions about ThreatWarrior, NDR, or how we work with CrowdStrike? Learn more about ThreatWarrior’s network detection and response and how it safeguards the enterprise.